19 May 2006
----------------------------------------------------------------------- To: jya[at]cryptome.org Cc: <A2[at]eff.org> Subject: Cryptome Google ads? And PayPal Date: Fri, 19 May 2006 16:09:44 -0700 From: A1 > Cryptome does have Google ads now, JY has sold out. '-) I didn't notice any Google ads (but I keep Javascript disabled, so maybe that spared me). I'd be surprised if there are Google ads on cryptome -- since that would mean that Google would have logfiles of every person who accessed cryptome, and what documents they looked at. Kinda makes cryptome's own log-deletion irrelevant. Which kinda puts cryptome's readership at risk. Without notifying them of the policy change. By examining the source of the main page, I see that indeed there are Google ads, and indeed they're behind Javascript (at the moment). Oh, my... However, it doesn't even take ads. There's a Google logo that gets loaded from a Google site -- regardless of the lack of Javascript. It's in the right margin near the top, which is why I didn't see it at first (it was off the right margin of my window). This gives Google a logfile entry every time someone accesses your home page, with a referer tag that shows them what page was accessed, and sends along the Google cookie if they are stupid enough to be carrying one. John, I bet there are even tools on the Google site that will let you examine who's accessing your site, how often, what pages they are looking at, whether they click through the ads, etc. If you don't believe me, that's the smoking gun that shows they're logging all these accesses. (And their stated policy is to log everything, keep the logs forever, and use them against the viewers.) I picked an HTML page at random from the index: dos051806.htm. This has no google image, so they can't track *me* to that page. But it does include Javascript Google page syndication, so 99.9% of the users will get tracked. Because they aren't smart enough to load the NoScript extention into Firefox, and control what sites are allowed to run JavaScript code in their browser. On the PayPal side, John, your site advertises it this way: "Make payments with PayPal - it's fast, free and secure!" That's a lie, actually, since it's not secure at all. PayPal "actively" cooperates with police agencies in tracking the movement of money of interest to the cops and spies. It isn't secure against some of the most important people to keep it secure against -- the ones whose crimes cryptome seeks to expose. I think if you even offer a PayPal option, you should make this clear to recipients. A1 PS: If you upload the 500MB NSA NYC video to the Internet Archive, they will be happy to host it, forever, for free, with 1.5Gbit/s of bandwidth (at the moment). Are you the copyright owner? If not, they'll need permission from the copyright owner.
A1, A2, There was a long, snarling, public discussion on Cryptome about Google ads, and warnings were posted about them and the host of ways snooping is going on, Google one among many. We're running the ads as a trial, they're on less than 1% of the Cryptome archive. I'll add your informative bitch about Google and PayPal to the file about other Net predators, a file I update and publish periodically. Thanks for sending, and send along other ways I can sell out, A2, I too am a professional. In exchange I bitch to you about log files, which I think are worse than Google, and cookies and spybots and maybe worse than the gov and biz spies for they are completely uncontrolled and those who gather them are accountable to nobody: nobody knows what is done with the data and its volume probably exceeds the telco hoard -- and they are easily harvested by a serious snoop who can zip right past site protection. I argue that no privacy policy is trustworthy by any site that keeps log files for any reason. There needs to be more ways to track usage without the use of log files, and the public needs to be alerted to the privacy hazard they pose by every site out there. My sense is that many goodhearted non-profits treasure their log data as much as gov and biz do. Sysadmins are the real snoops for Google and everybody else, and their argument the logs are needed to run the system is exactly what the gov and biz turkeys claim. For the protection of the users, hah. I'm not getting much traction for a campaign to ban log files and it would be great if EFF took this on again. I know there was an EFFort few years back to develop public-protection policy for to counter abuse of log files but it appears to have fizzled. The NSA video was made by me, no fear of copyright. I sent a copy to EFF and a few other goodhearts.
Here's the Google and PayPal snarling from February and March 2006:
March 2006
Cryptome Yarp: The Google ads will remain for a while.
The ad for TSCM.com, a scarily informative site, is a
trial run on the Cryptome server. Viewing it here is only in our logs, clicking
it is in TSCM.com's. [TSCM ad now gone.]
Visitors are strongly encouraged to anonymize net-surfing, not only to avoid
being logged by Google but by any
other means -- open and secret -- of snooping web sites and other communication
systems, by governments and even
more so by commercial and individual data miners. As reported yesterday in
the NY Times, intel agencies like
NSA are adopting less-regulated practices long-used for commercial purposes,
and private snoops have always
been criminals -- many of these are former spies and cops engaging in domestic
rendition. All blame the others
and "the enemy," lately, "the terrorists" to divert attention from what they
are doing; that, too, is a long-standing
practice.
Protect yourself, and don't leave privacy to illusory and deliberately deceptive
privacy policies, and don't believe law
enforcement and national security justifications for snooping-cloaked secrecy
laws.
Site visit logs and advertising on the Net are surely a greater threat to
privacy than government snooping. Site visits
and ad-viewing and -clicking data are the golden goose of site operators,
the Net's dirtiest secret and use and abuse
of them are completely unregulated, and corrupting because not being available
for visitor inspection -- a version of
corrupting national secrecy practices: "too important to allow public to
know because the enemy would know, the
logs have to be withheld from competitors and to protect visitor privacy,
and so on." Hey, who empowered site
operators to keep logs secret? Right, the sysadmins did themselves, kissing
up to bosses, kicking down to customers --
call them secret spies.
Suggestions that Cryptome offer ads from its own server to protect visitor
privacy presumes the server and its logs are
secure, when they are not, or that the Cryptome operator is trustworthy,
not true either, as we have often stated. We
delete logs, but the NTT/Verio server is located in Virginia. US agencies
are known to have easy access to all the
equipment in the facility, and, as noted here now and then, NTT accepted
as a condition of its purchase of Verio
that the FBI could have ready access to its networks. Who else has access,
gov or com or crim, is likely worse --
remote hacking and tapping a server -- legal or illegal -- is very easy,
Cryptome's server has been hacked before,
and there is nothing to prevent a recurrence nor is there any assurance that
it is not continually data-mined.
Cryptome has an offer to buy advertising across the top of this page,
and we're thinking of replacing the Google
banner with four 125 x 125 commercial banners ads. Comments on the privacy
impact? Send to jya[at]cryptome.net
__________
A4 writes:
The impact will depend on how the ads themselves are served, and what links they contain.
(1) If the ads are served by Cryptome, there will be no additional privacy implications for the pages on which they appear.(2) If the ads are served from a third-party URL, privacy will be less.
(3) Privacy will always be affected by the ad link when clicked.
The common issue between (2) and (3) lies in the nature of the third-party content-source or link-target URL respectively. If this URL is unique to a Cryptome ad, then the third-party receives information that a given hit is referred from Cryptome. If it very clearly isn't unique to Cryptome (generic URL like http://www.spacewar.com/) then in most cases the only 'technical' privacy leak is the HTTP "Referer" header, which can be plugged various ways. The risk of going to the third-party site of course remains.
My suggestion: Serve the ads from Cryptome, and bill your advertisers for the bandwidth they eat. Embed their link in a redirector running on your site, to sterilize the "Referer."
__________
Related report from spacewar.com:
We consider Google's action as an attempt to dictate what information will appear on Web sites, and what links will be allowed between Web sites. If true, this constitutes a gross abuse of market power, and it should cause our political leadership in the United States, Canada, Europe and Australia to investigate fully the business operations of Google Inc.We are deeply concerned about retaliatory action by Google Inc. against our company and its various Web sites. In recent months, we have bet the business on Google advertising revenues, which has left us dangerously exposed to major revenue losses should Google cancel our AdSense contract, and delay payments and/or sue us for going public.
-- Simon Mansfield, Google Inc, Bans Australian-based Military Space News Website, February 24, 2006
__________
A3 writes:
Who wants your banner ad space? Some front company for the CIA?
Many observers, including myself, felt in 1995 that search engines were going to cause major privacy problems, and the pubic was foolhardy to trust so much personal and business information to them. Of course all that is now part of the modern angst factor. We also send and receive most of our e-mails using using passwords sent in the clear, trusting that all will remain private.
My point being that whoever wants your banner ads, as long as they're not a CIA front, can't be much worse than Google. And if you can get up-front committed payments, based on average traffic, not per click-thorugh, you'll probably do much better financially.
One thing that might help a lot is if YOU could serve the ads, rather than the advertizer, thus NOT exposing everyone's IP address! Or at least have the ad serving done by a genuinely neutral party, such as doubleclick, assuming they won't get heavily filtered. Or try to demand an agreement not to retain logs of everyone's IP addresses, for more than say 10 seconds.
I still think you should be running ads for Anonymizers! Maybe you can do that down the side.
__________
A2 writes:
You're a lot more forgiving than me here. Adsense told me to bugger off on one of my sites, and the next thing I did was update robots.txt to exclude googlebot. I understand what you did, but the only way that Google is going to realize that their policy is asinine is to make sure that an Adsense rejection is permanent, no matter what happens later. As for privacy implications, you actually have illusions still on that point? How quaint.
__________
A writes:
You suggest readers use anonymizer.com if your site is blocked. However, Anonymizer.com is very limited. A better choice is Anonymouse.org
February 2006
A 5 writes:
A whole lot of hours go into making the cryptome sites work. Who pays for that? Are readers who object to the Google ads offering to send money? If they are, I don't see it. And what do these readers do for a living? You know, to PAY THE BILLS? Are they, for example, working for companies that may, in some way, be contributing to surveillance, to war-making, to toxic effluents, to bigger government, to the heap of useless little consumer items that keep the endless buying-crap mentality in full bloom? Are the people who object to the Google ads all saints busy saving the world full-time? Maybe Young should respond to these puerile objections by requiring that every visitor to his site fills out a complete profile first, to assure him that only absolute purity of mind and heart enters.
Cryptome: We'll think about that, too. The enticing ads on Cryptome.CN have been censored.
Daniel Brandt (google-watch.org) writes:
If you decide to forego the filthy lucre from Google but still want the search functionality you are currently testing, use our Scroogle Scraper proxy. We have no cookies, no search terms records, and our access logs are deleted within 48 hours. There's sample HTML at http://www.scroogle.org/masters.html that shows webmasters how to set up a site search box on their pages.
Google, as you must know, never deletes anything. They have recently admitted to inquiring journalists that they have the capacity to pull up a history of search terms by either the IP address, or by the unique ID in their cookie that expires in 2038. I've been screaming about this now for five years, but it's only in the last two months that no one has hurled the "tin-foil hat" slur at me. That's because of all the attention focused on the U.S. subpoena for Google's search-term information.
At last, everyone is waking up and saying, "Wow, I had no idea that they saved all that stuff!" Duh.
A4 writes:
With the recent concern for the Google Ads, maybe you could point out using TOR: http://tor.eff.org/ . I'd also like to know what if any visitor logs you keep, and if you keep them, for how long they are kept on your server.
Cryptome: Logs for all Cryptome sites are deleted daily, more often if traffic is heavy.
A3 writes:
Well after seeing the GoogleAds on the Cryptome site, I decided to add my opinion. I know many people, including myself, are grateful for all the time that is put into the cryptome.org and related sites, and not everyone appriciates that bandwidth, etc doesn't just grow on little trees. I think you're doing well to INVESTIGATE the potential of utilizing GoogleAds on the site, but there is one thing that now concerns me... As "A" nicely points out "it lowers the standard of privacy for visits to your site, and makes the question, "What addresses have visited Cryptome's front page?" answerable by the third-party server." Although I agree with him 100%, what worries me is what is next. If cryptome is willing to lower security & privacy (even by a bit) of its users now, what is next? Surely there is a way to generate some profit some other way.
Cryptome: $115 of villany so far, with the ads on about 60 files out of 33,000. Ads on the main page appear the most objectionable so we'll think about keeping the main page free of Google ads, with new files kept ad-free for a few days, say a week or so before ads are inserted. A major chunk of bandwidth is used by accesses for archival material, and a big chunk of that coming from Google searches, so maybe ads will only go on archival files. The current DVDs are free of ads, hint; but to get one you have to give a mailing address, to us, not Google. There are regular requests for a Cryptome search feature, so that will probably remain. The ads will be tried for a week or two see if they are worth keeping . If not, the contaminated files will be purified. Protect your privacy by staying away during the trial period. Best, keep away from the Net and other enlightenment pimps, climb a desert mountain and rot there awaiting levitation. To answer another question, we use anonymizer.com, one of the earliest, set up by Lance Cottrel in 1995 -- despite the risk all anonymizers are snooped by the evildoers. There is, or was, free code on the Net to set up your own anonymizer to cloak the first hop. And Google! IP-address cloaking methods, there are many of them. Try http://anonymouse.org/anonwww.html
A2 writes:
Although I object to your inclusion of google adsense ads on cryptome.org I can see your motivation (ca$h). However, it downright insulting for you to include the ad sense banner on cryptome.cn. Adsense inclusion is a disservice to the readers of cryptome.cn. It indicates that cryptome.cn is not sincere in its motives behind the site, nor is it respectful of the privacy of its visitors.
Cryptome: The Cryptome.cn ads today show the New York Times milking interest in PRC censorship which it advidly covers with lingerie ads galore:
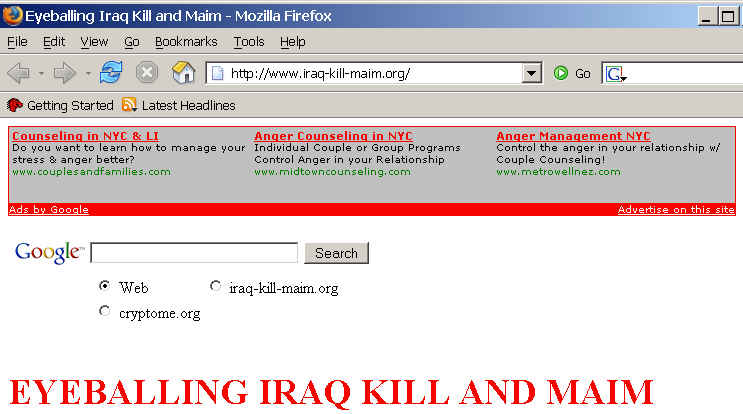
Cryptome: Good criticism, and we'll think about it. So far, $54 of corruption. We're testing the Google ads on four Cryptome sites and a dozen or so files. Ads being assigned by Google based on content change over time and vary by countries and the geo-location of the browser (the ones I see are aimed at New Yorkers); some are bizarre. For Iraq-Kill-Maim.org, which offers 4,000 photos of bloody carnage, here are the ads:
A writes:
I object to the inclusion of Google-served content on Cryptome's front page, for the same reason that I objected to a Paypal-served graphic there in 2004 -- it lowers the standard of privacy for visits to your site, and makes the question, "What addresses have visited Cryptome's front page?" answerable by the third-party server.
__________
Cryptome: Very well, we'll think about that during the trial run, and see what can be done about it. Your warning should be heeded by readers to avoid the site until then. Use of anonymizers is strongly encouraged. Cryptome issues periodic warnings about being snooped, locally or upstream, as with all other Internet sites and means of communication, usually by hidden means and always for the benefit of the service provider at the expense of the user. No site administrator or service provider or telecommunications corporation or media outlet is to be trusted with user data, none, this one included. Privacy policy is a fraud -- the louder the privacy protection brag the more likely the deception. Until site visit logs, telecommunications logs, media subscriber and purchasing lists are banned, you are at risk of being data-banked and exploited. Until use of the Internet and any means of communicating ends, reading and viewing TV stops, and buying products, making financial transactions, loving, living and dying are chucked, there is no privacy. Still, its worth pushing back and demanding the ripping and deceiving be reduced, or at least exposed and shamed, however futile the protests. So we trudge on across the desert under the watching and drooling vultures, satellites above, taps on earth and undersea, pillow mates salving tongue-flaps. Hiccup, burp.